Integrations
Connecting SecureSlate & AWS Organization
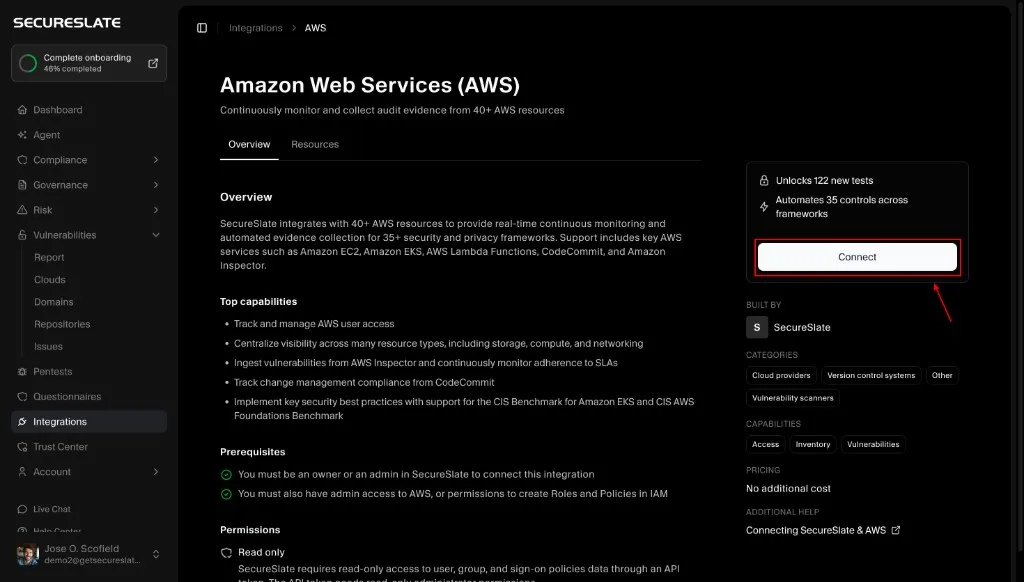
Connecting an AWS Organization to SecureSlate lets you continuously monitor all AWS accounts in your organization (including new accounts you add later). SecureSlate connects with read-only permissions and does not modify your AWS resources.
After connecting, findings appear on the Checks tab of the Cloud overview page, filtered by AWS.
AWS Account vs AWS Organization (what’s different?)
- Scope
- AWS account: connects one AWS account at a time.
- AWS organization: connects all accounts in your AWS Organization and automatically picks up newly created accounts.
- Setup effort
- AWS account: create one policy + role in a single account, then link the Role ARN.
- AWS organization: you typically repeat the policy + role creation for each member account (and may also need additional setup in the management account).
- When to choose
- Account: best for small environments or a single AWS account.
- Organization: best when you want centralized visibility across multiple AWS accounts.
Prerequisites
Before you start, make sure you have:
- SecureSlate permissions: access to create/manage integrations (typically Admin).
- AWS permissions:
- Ability to create customer-managed IAM policies and IAM roles in the AWS accounts you want to scan
- Access to your AWS Organization management account, if additional org-level configuration is required
Connect an AWS Organization (Console)
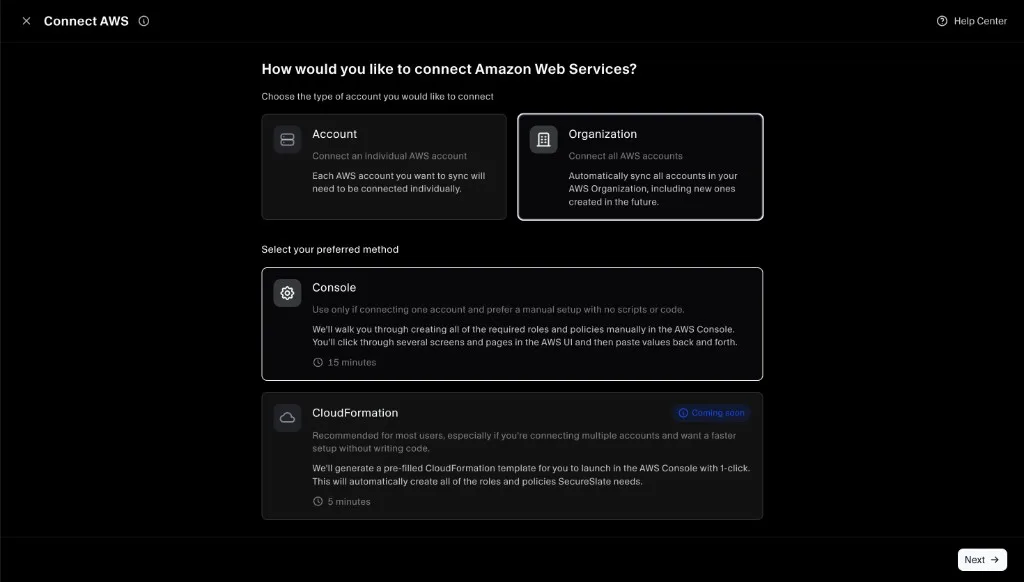
SecureSlate currently supports connecting an AWS Organization via the AWS Console (manual setup).
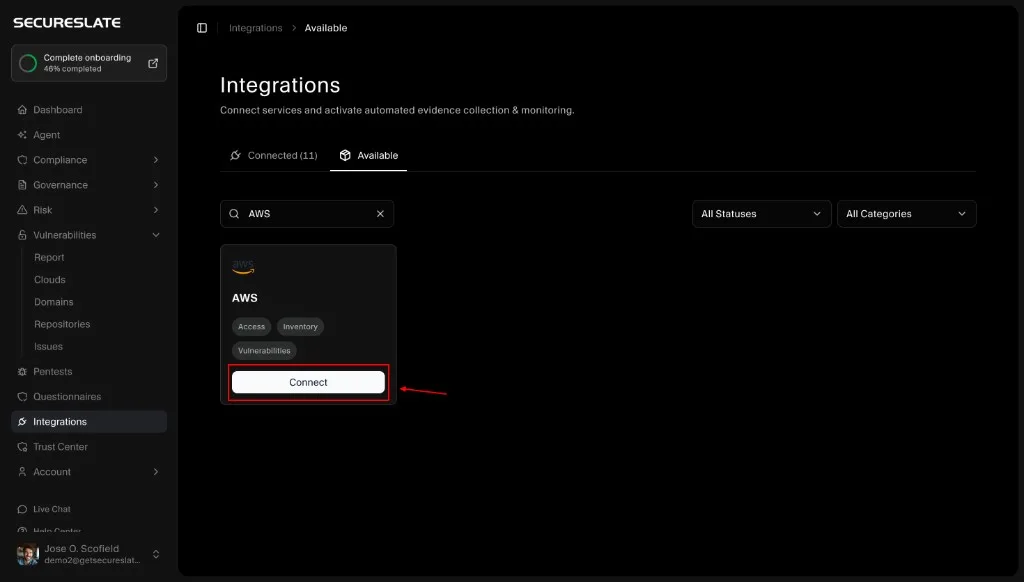
Step 1: Start the AWS integration setup
- In SecureSlate, go to Integrations.
- Open the Available tab.
- Search for AWS.
- Click Connect on the AWS card.
Step 2: Choose Organization + Console
- Select Organization.
- Under Select your preferred method, choose Console.
- Click Next.
Step 3: Select products to monitor
Toggle on any additional products you want SecureSlate to monitor. Your selection determines what permissions SecureSlate will include in the IAM policy you create.
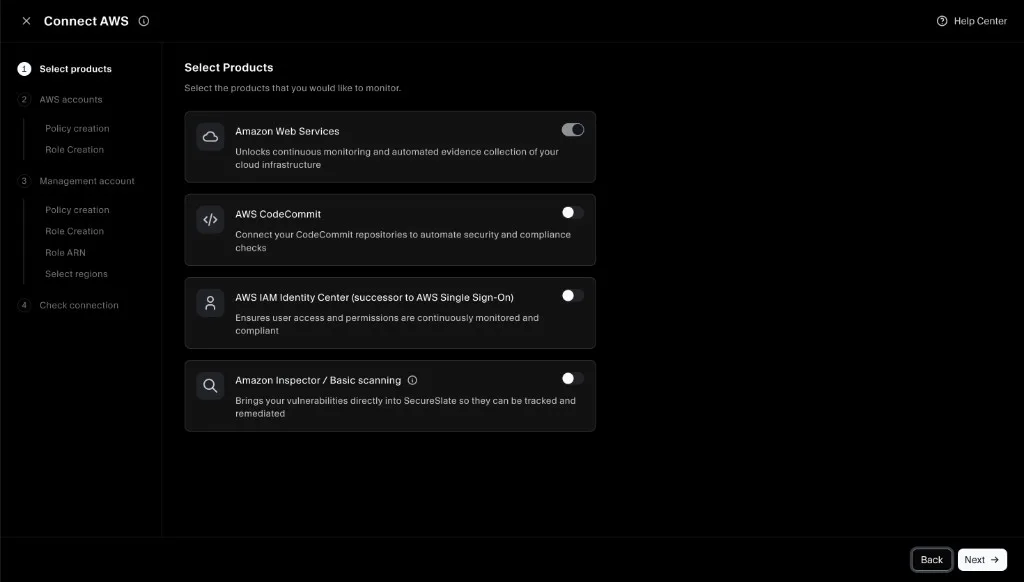
Organization flow overview
When connecting an AWS Organization, SecureSlate guides you through two parts:
- Member accounts: create the required policy + role in each member account you want to scan.
- Management account: apply additional permissions in the management (root) account so SecureSlate can discover accounts in the organization.
The AWS Console steps for policy/role creation are the same as the individual account setup, so this guide reuses those screenshots where they match.
Step 4: Member accounts: Create the IAM policy (repeat for each member account)
In the SecureSlate wizard, you’ll see a banner reminding you this step is for member accounts only.
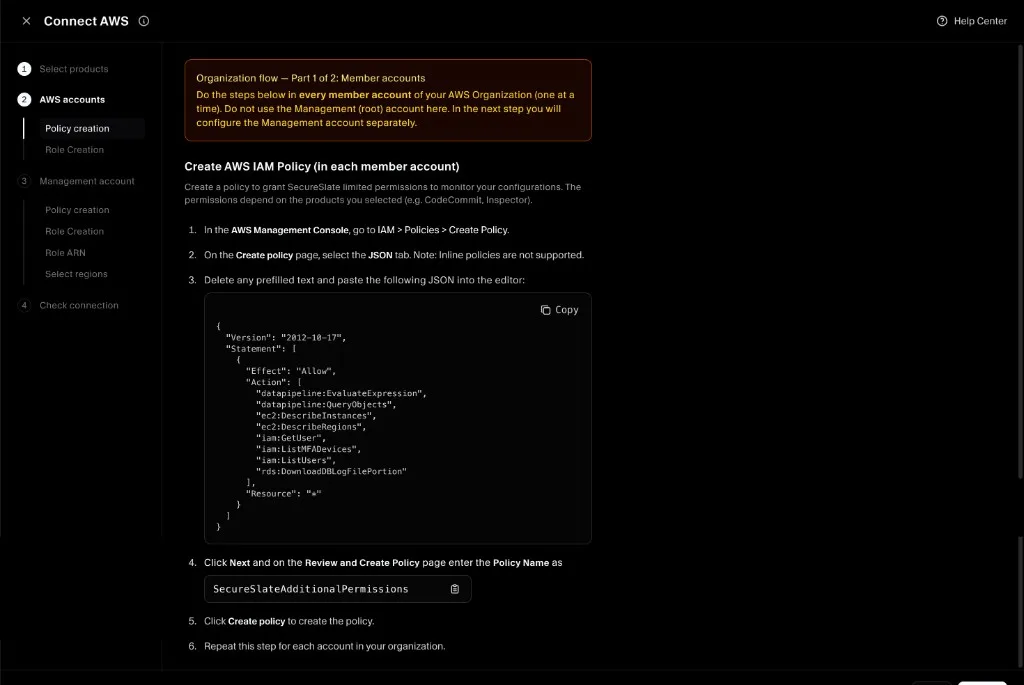
For each member account you want SecureSlate to scan:
-
In the SecureSlate wizard, copy the policy JSON.
-
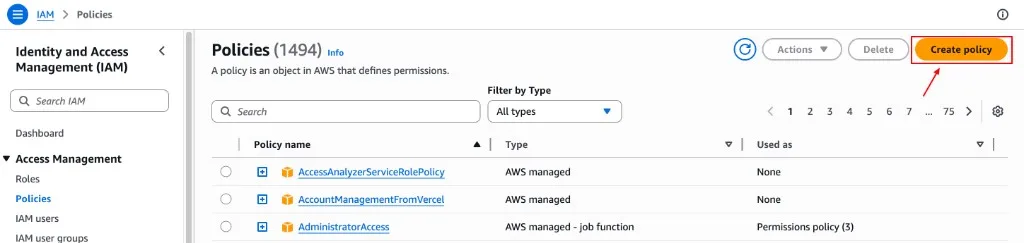
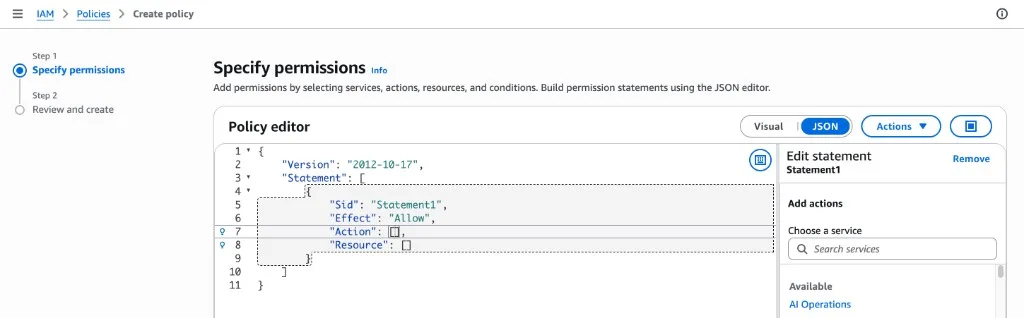
In the AWS Management Console, go to IAM → Policies → Create policy.
-
Open the JSON editor, delete any prefilled text, and paste the policy JSON from SecureSlate.
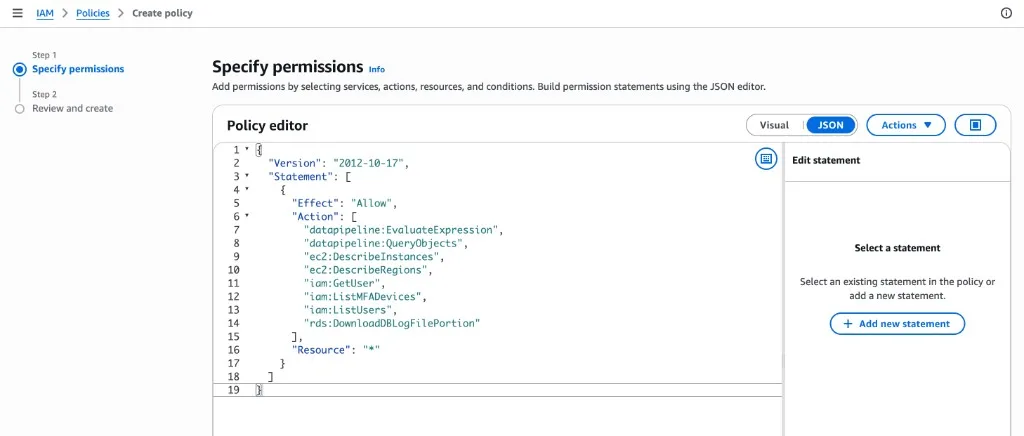
-
Click Next, then name the policy SecureSlateAdditionalPermissions.
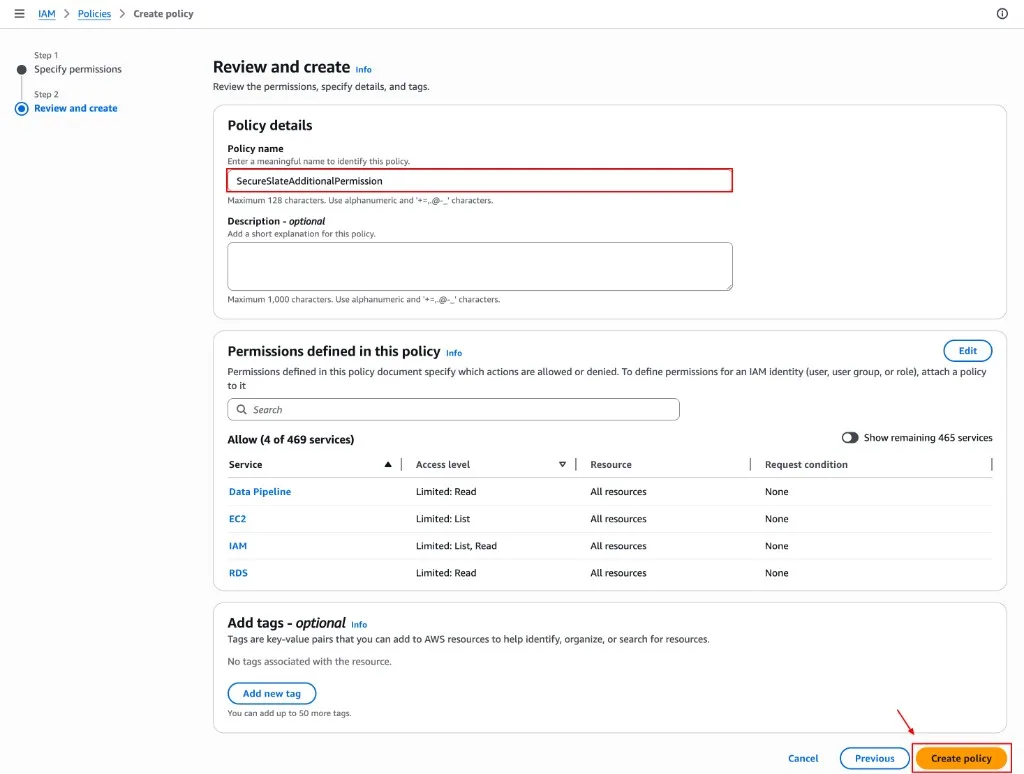
-
Click Create policy.
Step 5: Member accounts: Create the IAM role (repeat for each member account)
In the wizard, you’ll also see a banner reminding you to create the role in member accounts only.
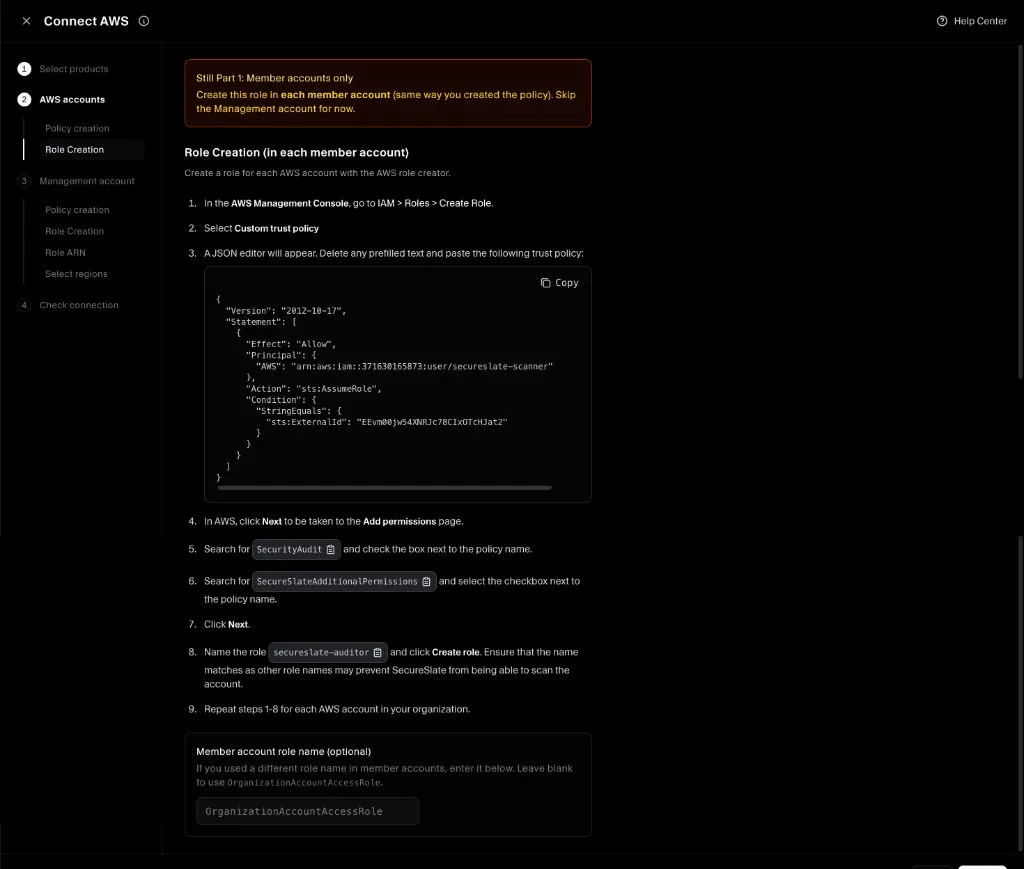
For each member account you want SecureSlate to scan:
-
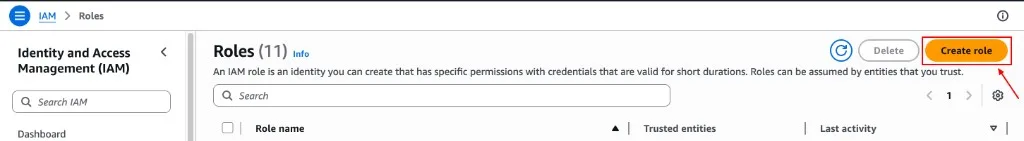
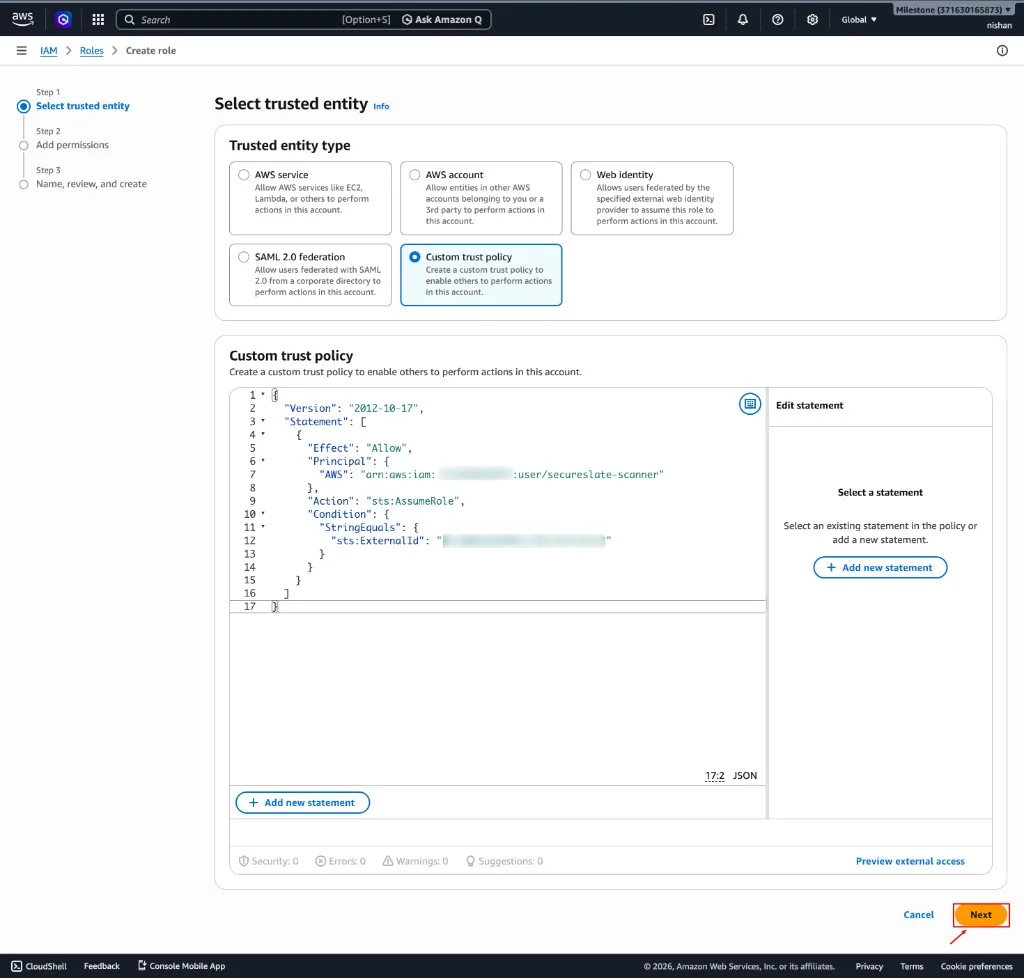
In AWS, go to IAM → Roles → Create role.
-
Select Custom trust policy.
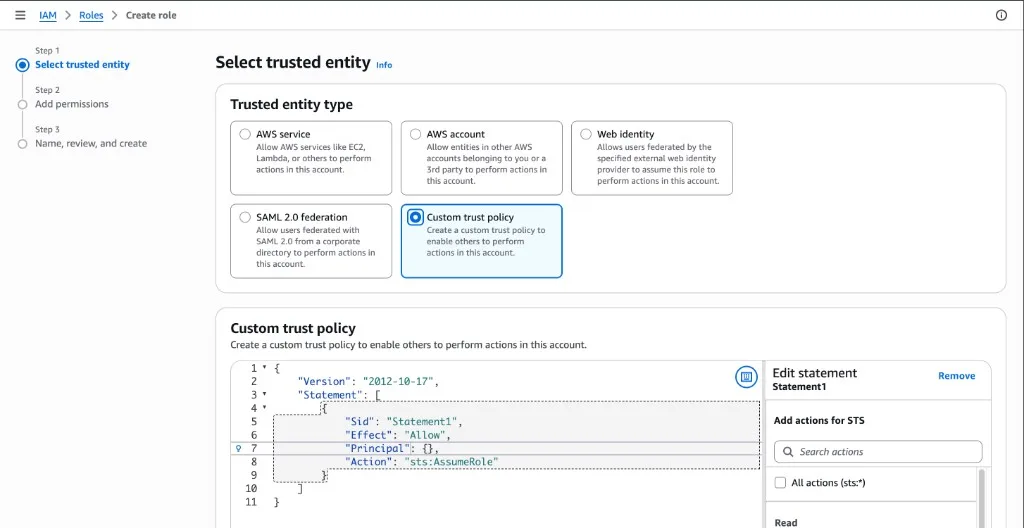
-
Paste the trust policy shown in SecureSlate (it includes a required External ID).
-
Click Next.
-
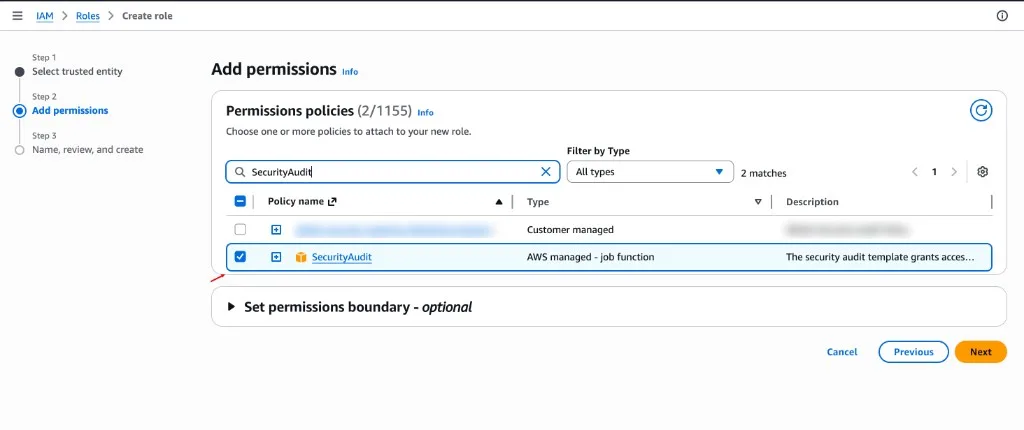
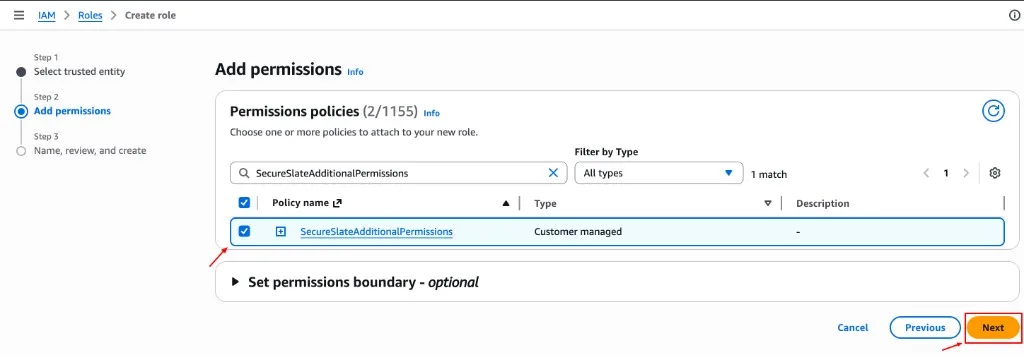
Attach both required permission policies:
- AWS managed policy: SecurityAudit
- Customer-managed policy: SecureSlateAdditionalPermissions
-
Finish role creation with the name secureslate-auditor.
Step 6: Management account: Create the organization policy
After member accounts are configured, SecureSlate will prompt you to configure the management (root) account. This step uses a different policy than member accounts (it includes AWS Organizations permissions so SecureSlate can discover accounts).
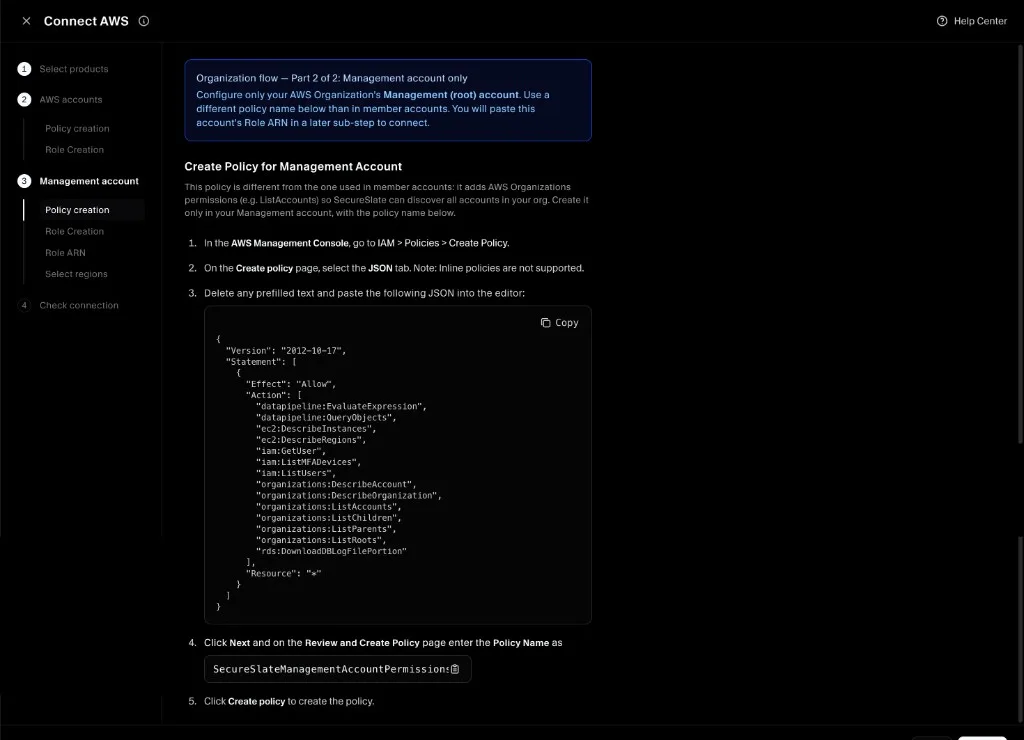
In your management account:
- In the SecureSlate wizard, copy the management account policy JSON.
- In AWS, go to IAM → Policies → Create policy.
- Paste the JSON and create a customer-managed policy named SecureSlateManagementAccountPermissions.
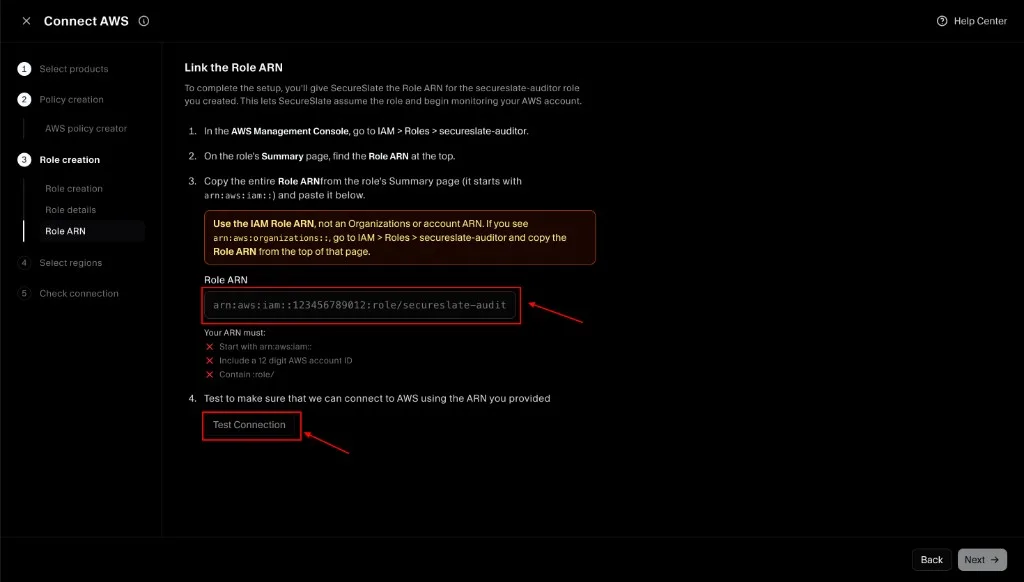
Step 7: Link the Role ARN(s) in SecureSlate
- In each AWS account (member accounts, and management account if prompted), open IAM → Roles →
secureslate-auditor. - Copy the Role ARN.
- Paste the Role ARN(s) into SecureSlate and click Test Connection.
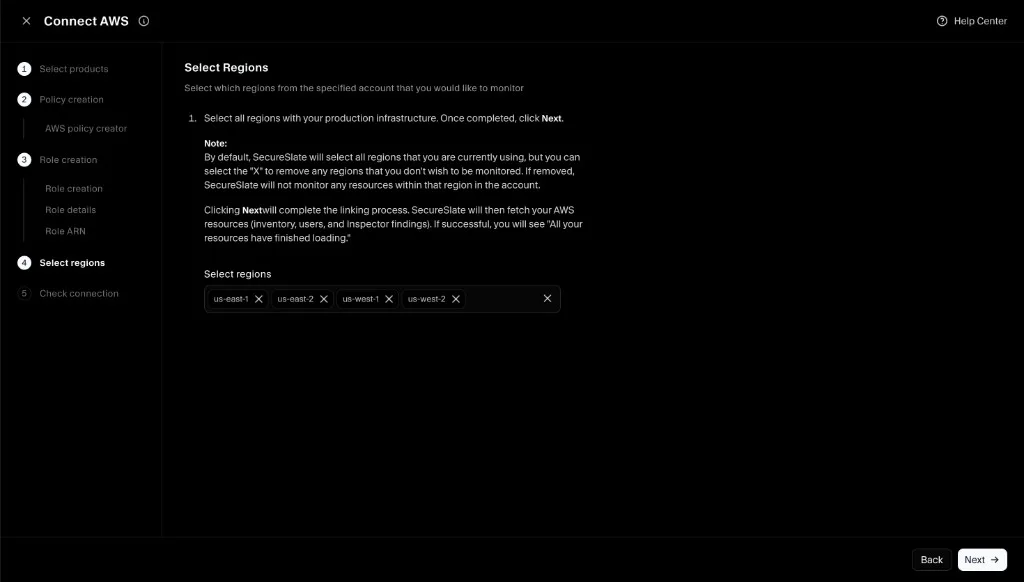
Step 8: Select regions (scope) and complete connection
- Select which AWS regions you want SecureSlate to monitor.
- Click Next to complete linking.
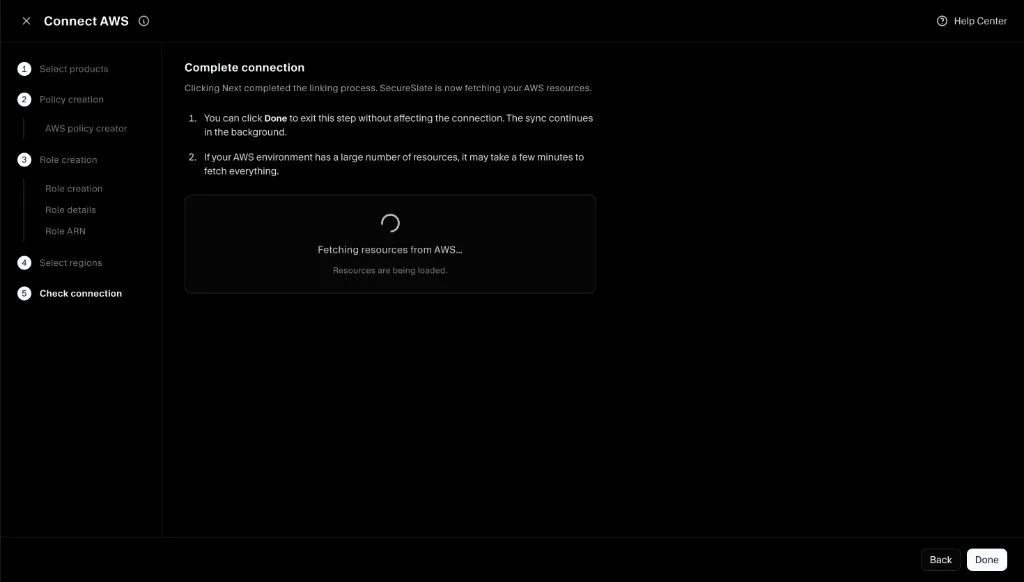
SecureSlate will begin fetching and scanning resources. Larger organizations can take longer for the initial sync.
Troubleshooting
- If a member account fails to connect, confirm that account has:
- The
secureslate-auditorrole - Both permission policies attached (SecurityAudit + SecureSlateAdditionalPermissions)
- The correct trust policy (including the External ID from SecureSlate)
- The