User Access
Access Reviews
Access reviews in SecureSlate help you regularly confirm that the right people have the right level of access to your systems—similar to access review features in other compliance tools, but fully integrated with your existing SecureSlate data.
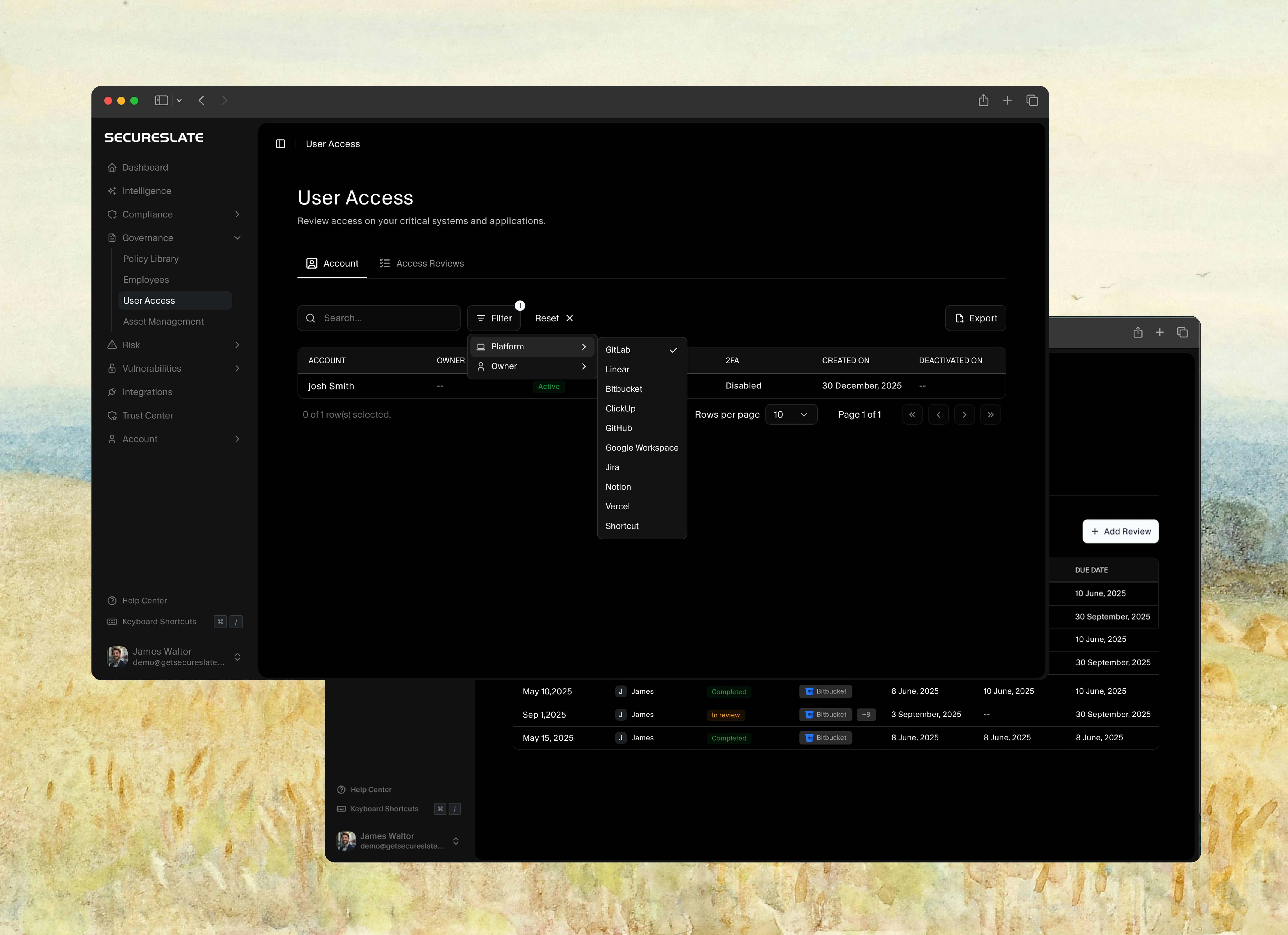
SecureSlate automatically pulls account access from your connected integrations into the User Access → Account tab. Access reviews use this data so you can periodically verify and document access decisions for audits.
Before you start
Make sure:
- Your key systems (for example, SSO/IdP, code repos, ticketing, cloud, HR) are connected via Integrations.
- Accounts in the Account tab have owners assigned wherever possible.
Open the Access Reviews page
- From the sidebar, go to User Access.
- Click the Access Reviews tab at the top.
At the top of the page you’ll see:
- A donut chart of systems by inherent risk score (High, Medium, Low, Unscored).
- Totals for each risk band to help prioritize which systems to review first.
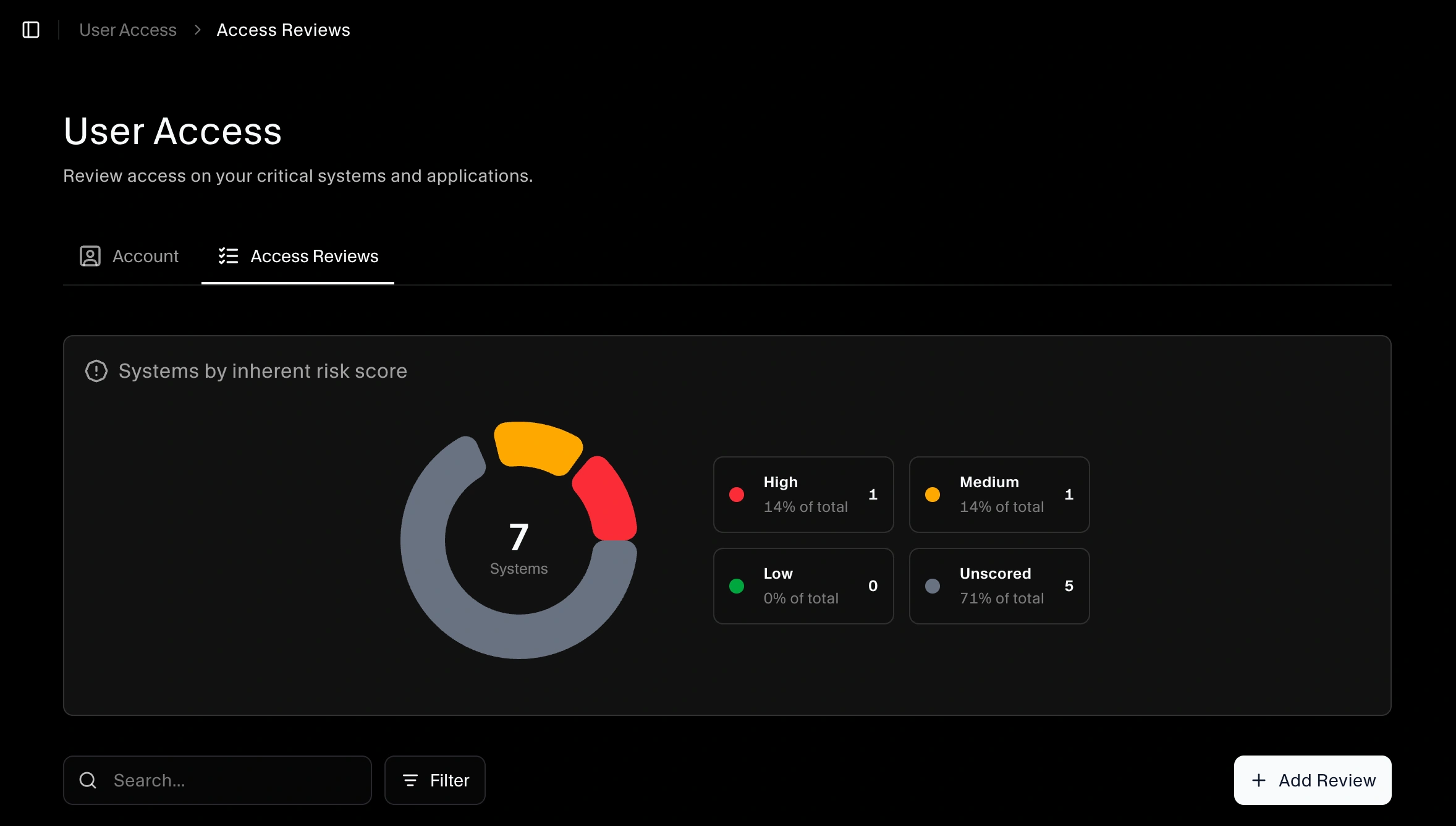
Below that is the reviews table with details like Review name, Reviewer, Status, Reviewing (system/vendor), Started on, Completed on, and Due date.
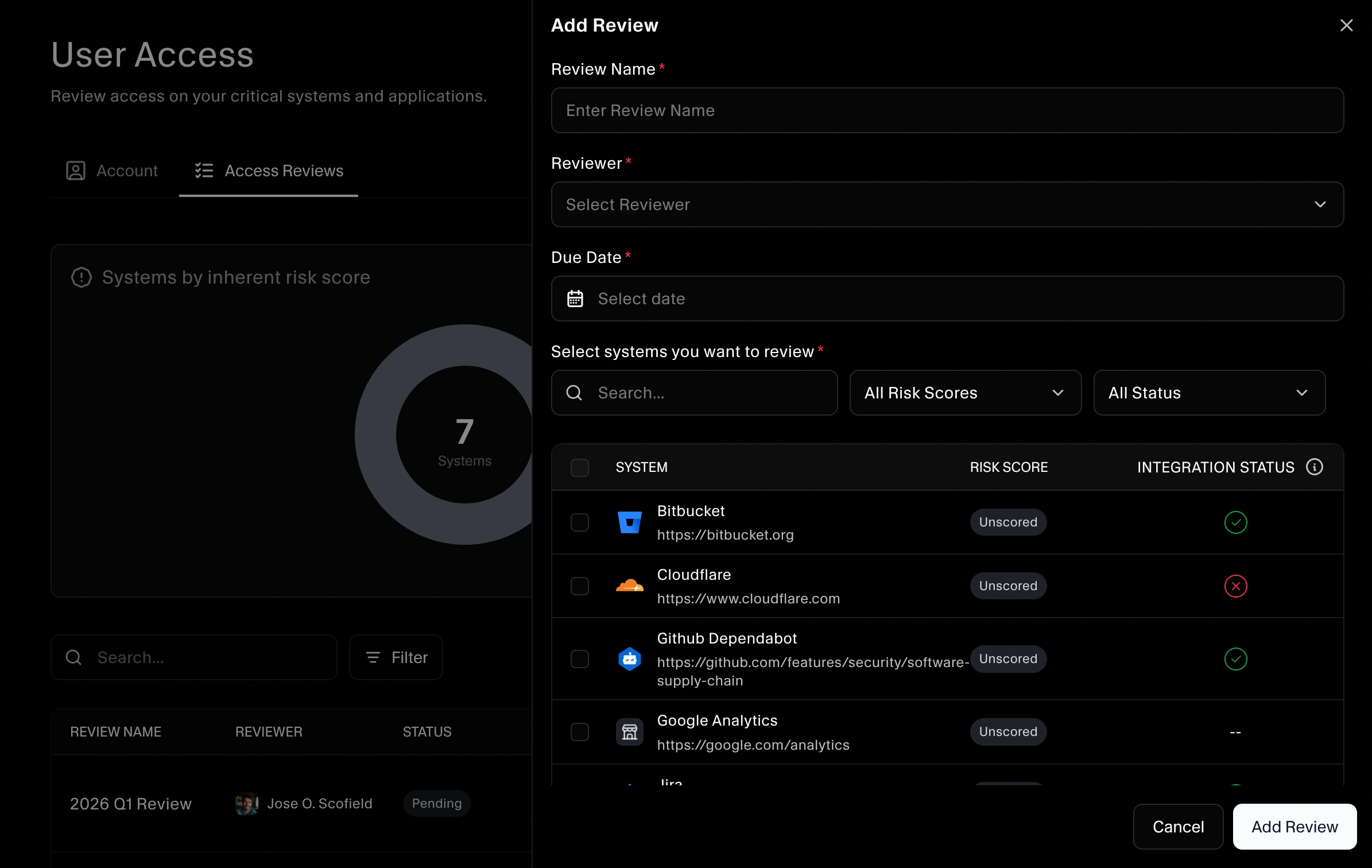
Create a new access review
Use Add Review to start a new review cycle.
- On the Access Reviews tab, click Add Review.
- Give the review a clear name (for example, “Q1 2026 Access Review – Production Systems”).
- Select the systems/vendors that will be in scope for this review.
- Choose a reviewer (the person responsible for making access decisions).
- Set start and due dates.
- Save the review to create it.
Once the review is created and started, the reviewer will see the in-scope systems and related accounts that need to be evaluated.
Reviewing access for each system
For each system included in the review:
- Open the review from the Access Reviews table.
- Click on Start Review to start the review.
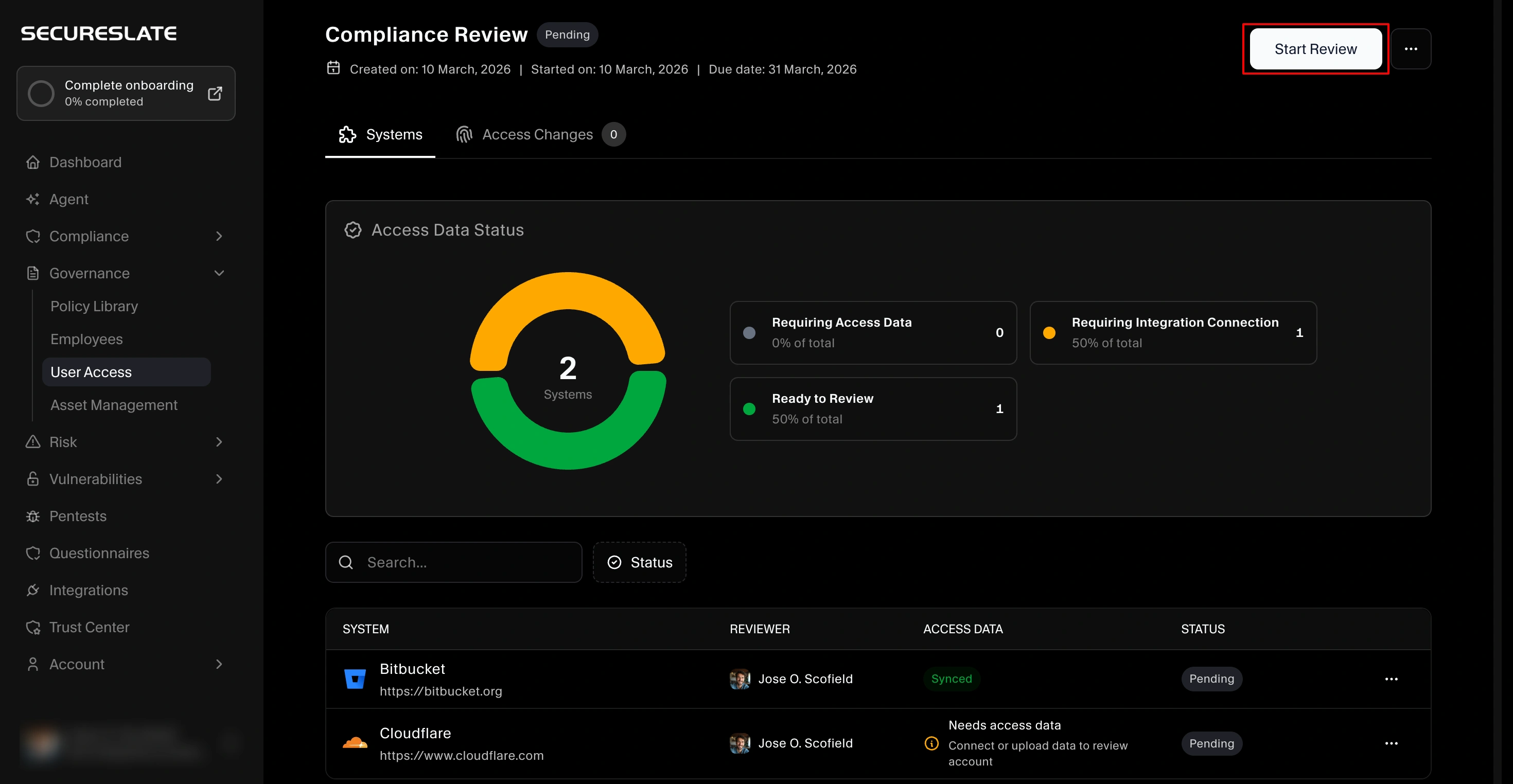
- Click a system/vendor in the review to view its accounts.
- For each account, the reviewer decides whether access is still appropriate, needs to be changed, or should be removed, based on the user’s role and least‑privilege principles.
- Optionally add notes to explain unusual cases or exceptions.
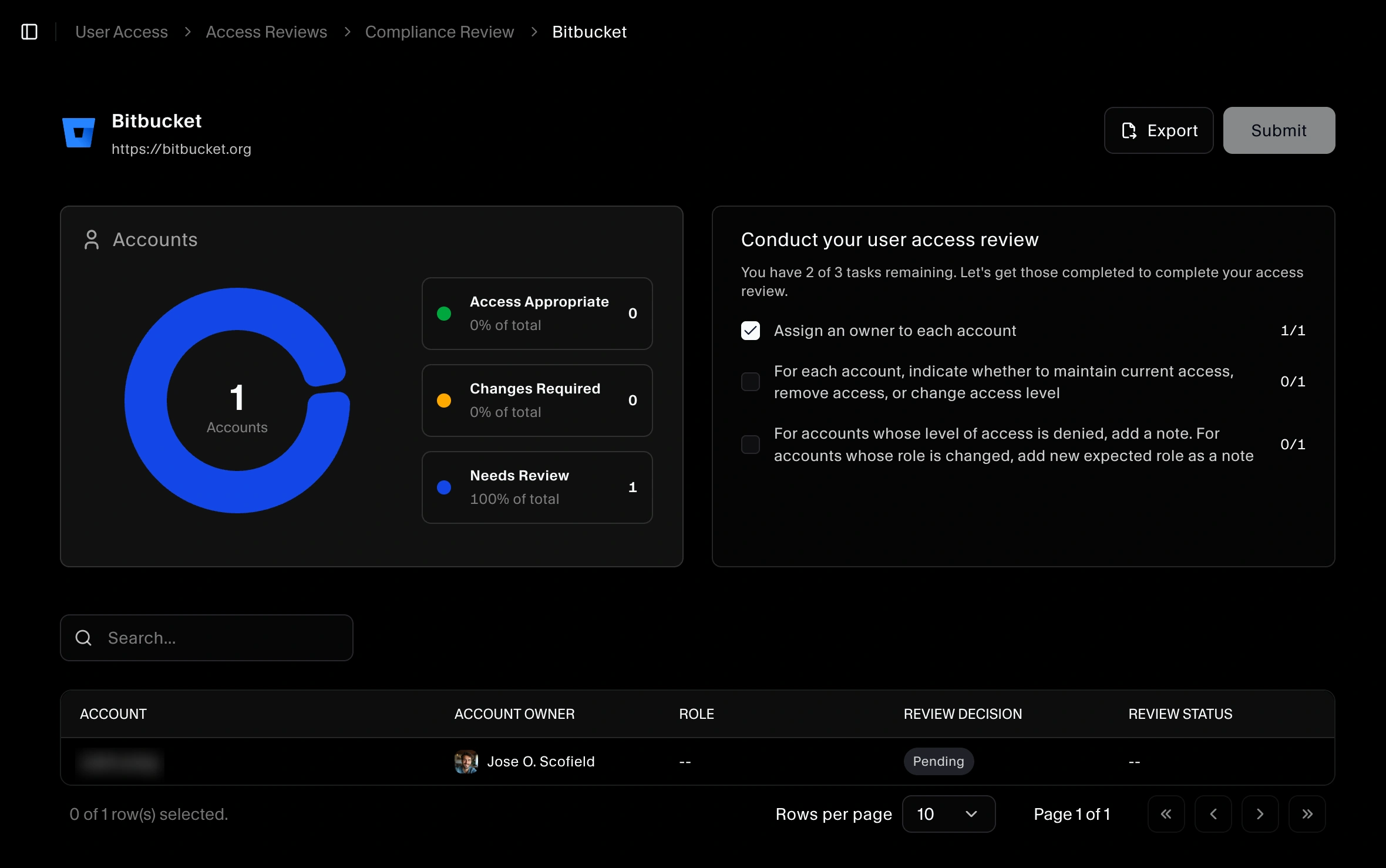
All accounts should have an owner assigned before the review is submitted.
Completing a review
When all accounts for the in-scope systems have been evaluated:
- Confirm that every account has a decision recorded.
- Submit or mark the review as Completed.
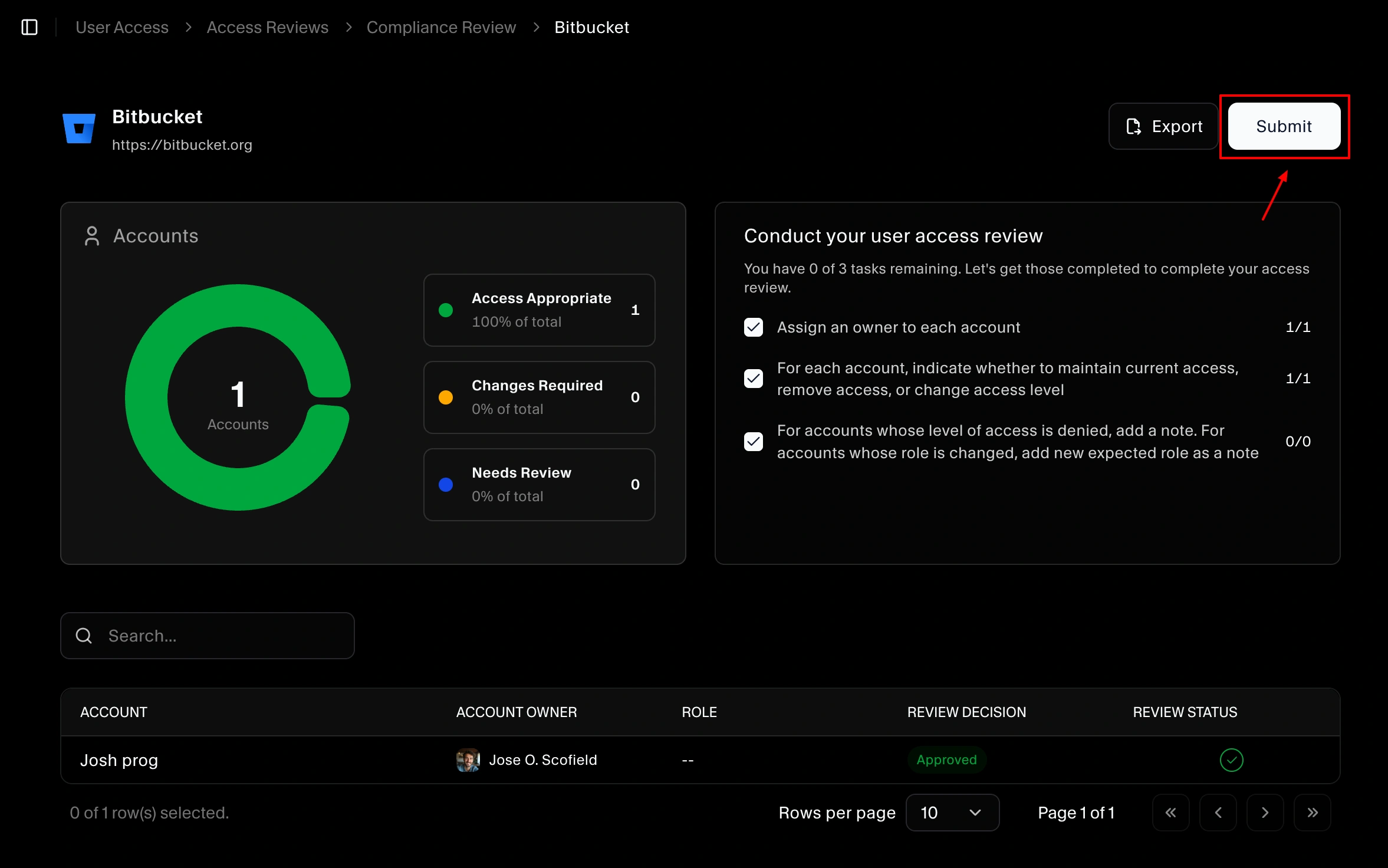
The completed review becomes part of your audit trail, demonstrating that you regularly verify user access across critical systems.
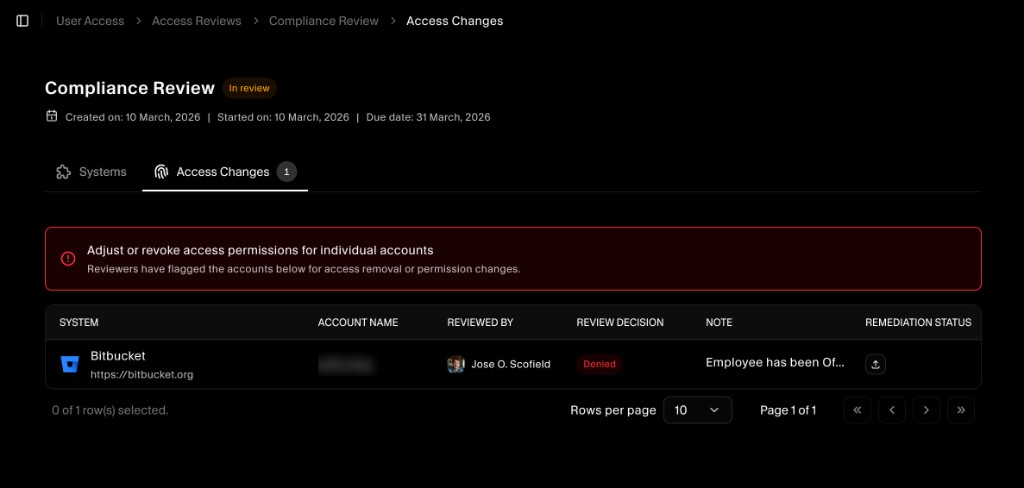
Access Changes tab: denied or changed roles
After a system review is completed, any account where the reviewer chose Denied (remove access) or Change role is listed in the Access Changes tab for that review.
From the review page, open the Access Changes tab to see:
- System: The integrated system (for example, Bitbucket).
- Account name: The account that was denied or had its role changed.
- Reviewed by: Who made the decision.
- Review decision: Denied or the new role.
- Note: Any comment the reviewer left.
- Remediation status: Where you provide evidence that the change was carried out.
A banner at the top reminds you to adjust or revoke access for these accounts in the actual system and to document remediation in SecureSlate.
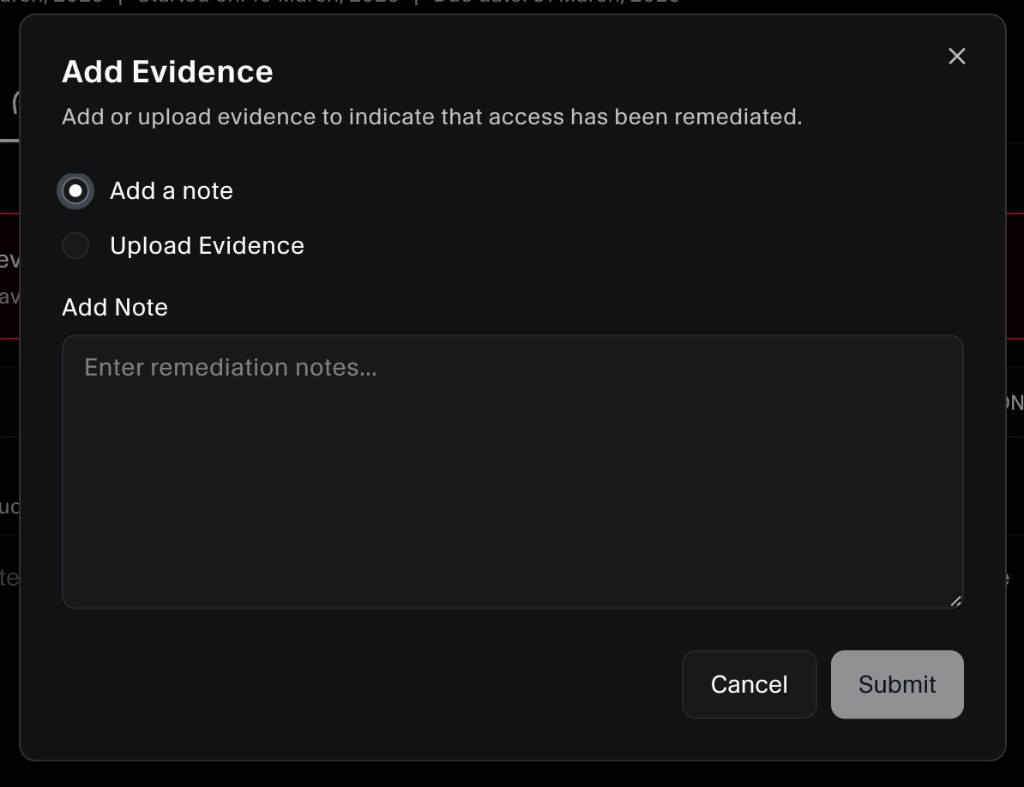
Providing remediation for access changes
For each account in the Access Changes table, you must provide remediation evidence so auditors can see that access was actually removed or updated.
- In the Access Changes tab, find the row for the account.
- In the Remediation status column, click the upload icon.
- In the Add Evidence dialog, choose one of:
- Add a note: Enter remediation notes (for example, “Access revoked in Bitbucket on 12 March 2026” or “Role updated to read-only in admin console”).
- Upload evidence: Attach a file (screenshot, export, or ticket) showing that the change was made in the system.
- Click Submit to save the evidence.
Once evidence is added, the remediation status for that account is updated. Repeat for every account in the Access Changes list so the review is fully documented.
Using review results
Access reviews themselves do not directly change permissions in your integrated systems. Instead, use review outcomes to:
- Create tasks to remove or adjust access where needed.
- Update roles or group memberships in your identity provider or application.
- Document remediation for denied or changed accounts via the Access Changes tab (note or uploaded evidence).
- Document exceptions and compensating controls for audit purposes.
You can export review data (using Export) to share with stakeholders, attach to tickets, or provide directly to auditors.
Best practices
- Schedule reviews at a frequency that matches your frameworks (for example, quarterly for SOC 2, annually for ISO 27001).
- Prioritize high‑risk systems (those with sensitive data or high operational impact).
- Ensure every account has an owner, so remediation is clearly assigned.
- Keep notes concise but specific enough that auditors can understand why access was kept, changed, or removed.
